The QUATTRO is one of the most flexible, efficient and compact lasers on the market. Many metal working companies have a large number of components to manufacture but only need to produce one or two at a time. Ease of use, plus low operating costs make the QUATTRO the ideal solution for low volumes, without forgoing precision and quality.
This machine is no longer available.
Find the laser machine that suits your needs
If you have encountered this file, it is highly recommended to:
: Recent security reports from platforms like BleepingComputer discuss how attackers use techniques like ZIP file concatenation to hide malicious code within seemingly normal archives to bypass antivirus scanners. HackClient.zip
: Legitimate hacking or modding clients (for ethical hacking or game modding) are typically hosted on verifiable platforms like GitHub, where the source code is public and reviewed by the community. If you have encountered this file, it is
"HackClient.zip" is a generic filename often associated with malicious software, particularly Minecraft "ghost clients" or "cracked" hacking tools that are used to hide malware. Security articles frequently highlight such files as vehicles for , information stealers , and ransomware . Common Security Risks For more information on identifying and avoiding malicious
: Hackers often name malicious archives "HackClient.zip" or similar to lure users looking for game cheats (like for Minecraft or Roblox). These files often contain Remote Access Trojans (RATs) that give attackers full control over the victim's computer.
For more information on identifying and avoiding malicious hacking tools, you can refer to resources on Ethical Hacking which emphasize the importance of using trusted sources for security tools. Ethical Hacking - Zenk - Security - Repository
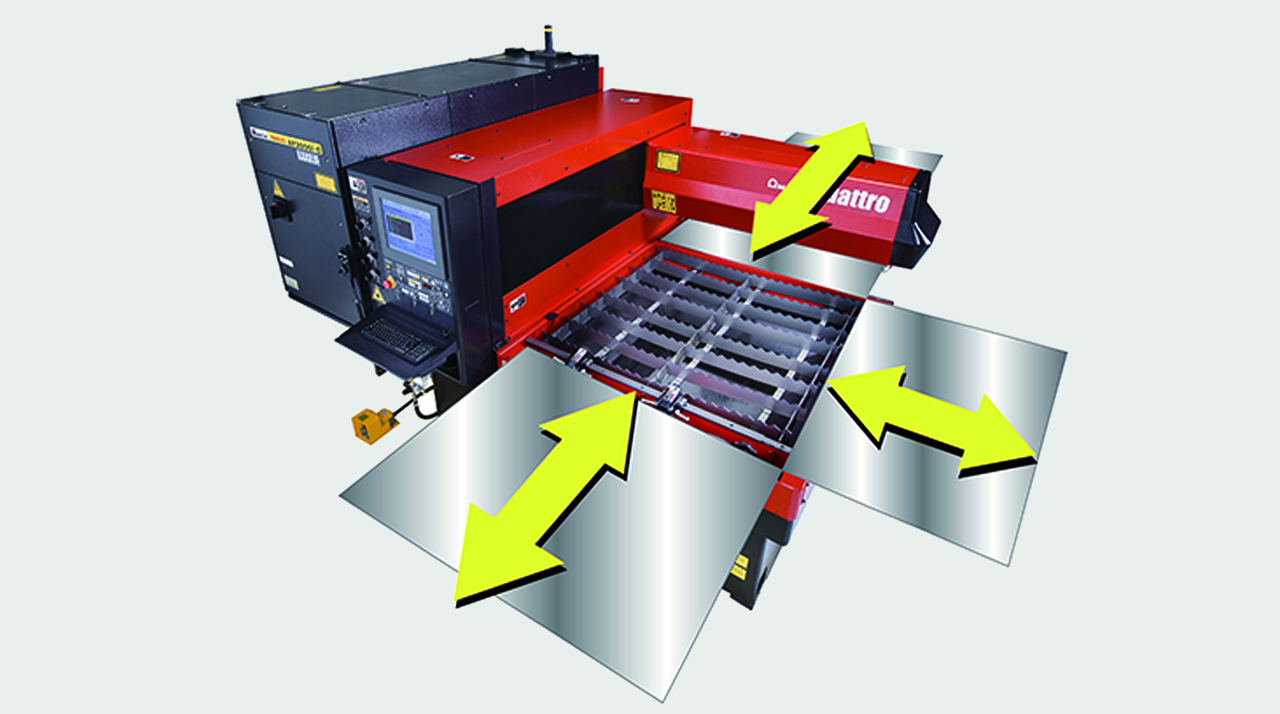
FULL ACCESS TO THE CUTTING AREA:
The three accessible sides of the QUATTRO laser facilitate sheet metal loading and unloading. Large-sized sheets which are bigger than the work area can also be processed, repositioning them manually.

COMPACT STRUCTURE:
With a footprint of just 6.4 m2, the QUATTRO is AMADA's smallest laser. The oscillator and numerical control are contained within the machine to maintain its extremely compact size.

DIVERSIFIED PROCESSING:
With the QUATTRO, not only sheet metal but rectangular and square tubes can be processed, providing even greater flexibility. (Option)

| QUATTRO | QUATTRO | |
|---|---|---|
| Laser power (W) | 1000 | 2500 |
| Machine type | CO₂ flying optic laser | CO₂ flying optic laser |
| Working range X x Y (mm) | 1250 x 1250 | 1250 x 1250 |
| Working range Z-axis (mm) | 100 | 100 |
| Table loading weight (kg) | 80 | 160 |
Material thickness (max.)*: | ||
| - Mild steel (mm) | 6 | 12 |
| - Stainless steel (mm) | 2 | 5 |
| - Aluminium (mm) | 1 | 4 |
Dimensions: | ||
| Length (mm) | 2900 | 2950 |
| Width (mm) | 2450 | 2450 |
| Height (mm) | 2160 | 2160 |
| Weight (kg) | 3750 | 4150 |
* Maximum thickness value depends on material quality and environmental conditions
Technical data can vary depending on configuration / options
Please contact us for more details and options or download our brochure

For your safe use.
Be sure to read the user manual carefully before use.
When using this product, appropriate personal protection equipment must be used.

Laser class 1 when operated in accordance to EN 60825-1
If you have encountered this file, it is highly recommended to:
: Recent security reports from platforms like BleepingComputer discuss how attackers use techniques like ZIP file concatenation to hide malicious code within seemingly normal archives to bypass antivirus scanners.
: Legitimate hacking or modding clients (for ethical hacking or game modding) are typically hosted on verifiable platforms like GitHub, where the source code is public and reviewed by the community.
"HackClient.zip" is a generic filename often associated with malicious software, particularly Minecraft "ghost clients" or "cracked" hacking tools that are used to hide malware. Security articles frequently highlight such files as vehicles for , information stealers , and ransomware . Common Security Risks
: Hackers often name malicious archives "HackClient.zip" or similar to lure users looking for game cheats (like for Minecraft or Roblox). These files often contain Remote Access Trojans (RATs) that give attackers full control over the victim's computer.
For more information on identifying and avoiding malicious hacking tools, you can refer to resources on Ethical Hacking which emphasize the importance of using trusted sources for security tools. Ethical Hacking - Zenk - Security - Repository